Project Objective
A geographically dispersed network built on hierarchical design using Layer 3 switching at each site, interconnected via routed WAN links, with comprehensive security policies and centralized management. The network supports NinjaPostal Corporation's operations across Toronto, Vancouver, and Tokyo offices.
Challenge & Adaptation
Successfully pivoted from BGP to EIGRP routing protocol due to physical hardware limitations, demonstrating adaptability and problem-solving skills while maintaining all functional requirements.
Network Topology
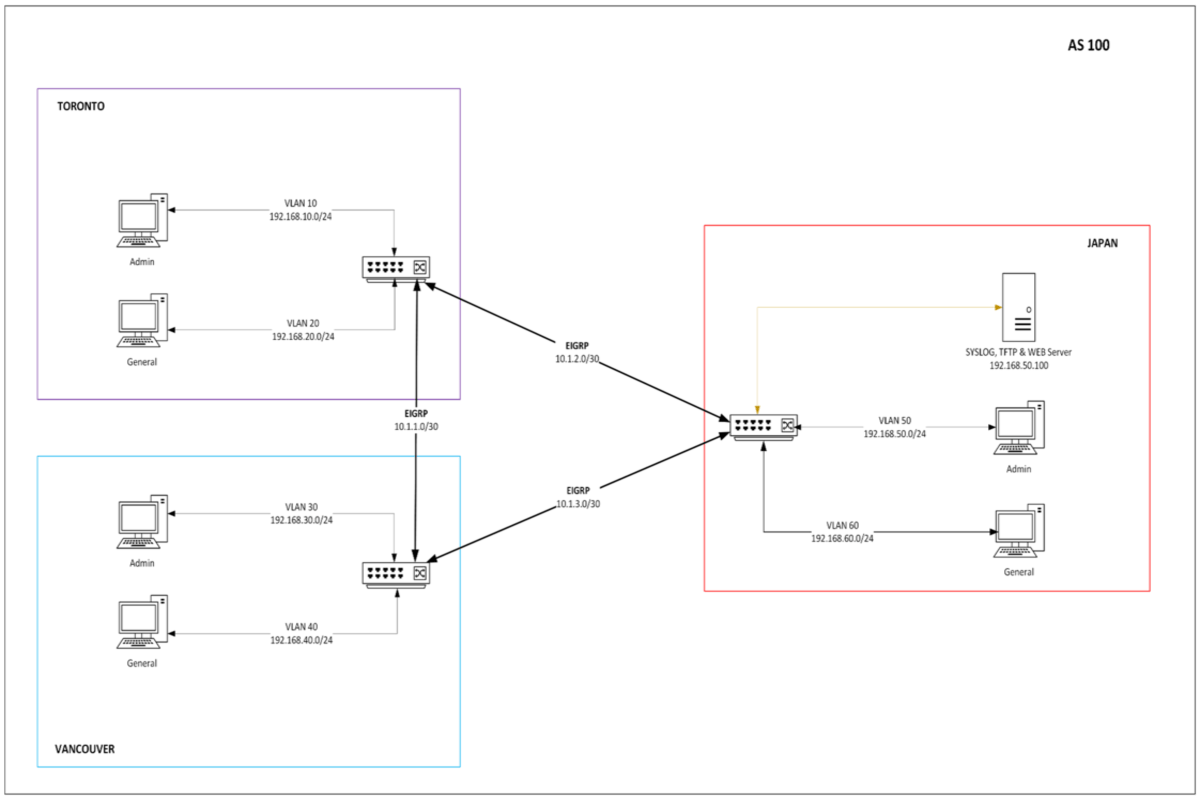
Site Architecture
Toronto (HQ)
Headquarters with Admin VLAN (192.168.10.0/24) and General VLAN (192.168.20.0/24). L3 switch with SVI for inter-VLAN routing.
Vancouver
Western Canada office with Admin VLAN (192.168.30.0/24) and General VLAN (192.168.40.0/24). Connected via 10.1.1.0/30 link.
Tokyo
Asia-Pacific office with Admin VLAN (192.168.50.0/24) and General VLAN (192.168.60.0/24). Hosts centralized services.
Centralized Services
Tokyo Admin VLAN hosts WAMP web server, TFTP for config backup, and Kiwi Syslog server for logging.
IP Addressing Scheme
| Site | VLAN | Subnet | Gateway (SVI) |
|---|---|---|---|
| Toronto | Admin (VLAN 10) | 192.168.10.0/24 | 192.168.10.1 |
| General (VLAN 20) | 192.168.20.0/24 | 192.168.20.1 | |
| Vancouver | Admin (VLAN 30) | 192.168.30.0/24 | 192.168.30.1 |
| General (VLAN 40) | 192.168.40.0/24 | 192.168.40.1 | |
| Tokyo | Admin (VLAN 50) | 192.168.50.0/24 | 192.168.50.1 |
| General (VLAN 60) | 192.168.60.0/24 | 192.168.60.1 |
Point-to-Point WAN Links
| Link | Subnet |
|---|---|
| Toronto ↔ Vancouver | 10.1.1.0/30 |
| Vancouver ↔ Tokyo | 10.1.2.0/30 |
| Tokyo ↔ Toronto | 10.1.3.0/30 |
Technical Implementation
Network Foundation
- Comprehensive IP scheme: VLAN subnets (192.168.x.0/24), P2P links (10.1.x.0/30)
- VLAN creation and SVI configuration for inter-VLAN routing on L3 switches
- EIGRP AS100 on all L3 switches (adapted from initial BGP design due to hardware constraints)
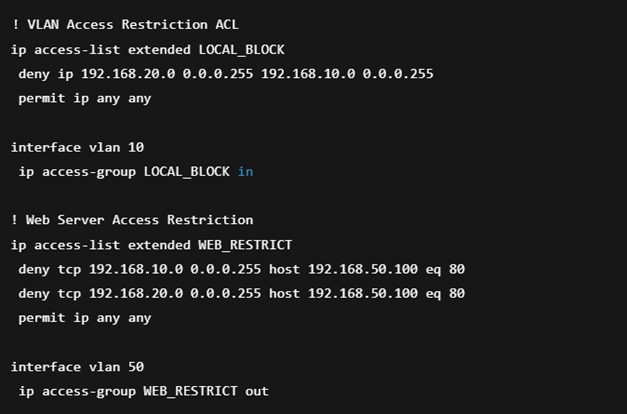
Security Policy Enforcement
- Extended ACLs for one-way VLAN access: General → Admin blocked, Admin → General allowed
- Service ACLs: HTTP to Tokyo server restricted to Vancouver Admin only
- Port Security: One MAC per port, sticky learning, restrict violation mode with syslog
- SSHv2 with RBAC: netadmin (15), techsupport (5), intern (1) privilege levels
Centralized Services
- WAMP web server for internal applications hosted in Tokyo
- TFTPD32 for configuration backups and firmware updates
- Kiwi Syslog Server for centralized logging from all network devices
- Syslog integration for all switches and port-security violations
Security Configuration
| Security Feature | Configuration | Purpose |
|---|---|---|
| VLAN ACLs | Extended ACLs on SVIs | General → Admin blocked; Admin → General allowed |
| Service ACLs | HTTP permit from Vancouver Admin only | Restrict web server access to authorized subnet |
| Port Security | Max 1 MAC, sticky, restrict mode | Prevent unauthorized device connections |
| SSH Access | SSHv2 only, VTY ACL | Secure remote management |
| RBAC | Privilege levels 1, 5, 15 | Role-based command authorization |
Testing & Validation
Reachability Testing
Inter-VLAN and inter-site ping tests across all permitted paths verified full mesh connectivity.
ACL Enforcement
Verified General-to-Admin blocking and web server access restrictions working as designed.
Service Testing
HTTP access, TFTP configuration backups, and syslog message reception validated.
Security Validation
Port security violations triggered and logged; RBAC privilege levels verified via SSH.
Project Gallery
Additional screenshots coming soon
Technical Highlights
Protocol Adaptation
Successfully pivoted from BGP to EIGRP due to hardware support limitations while maintaining full functionality.
Defense-in-Depth
Implemented layered security with VLANs, ACLs, port security, and RBAC following least privilege principles.
Sim-to-Physical
Translated simulated Packet Tracer design to working physical Cisco switches, overcoming software limitations.
Technologies Used
Network Design
Cisco IOS
Routing Protocols
Network Security
Network Services
Tools
Project Outcomes
- Built fully functional, secure, policy-driven enterprise network meeting all requirements
- Successfully pivoted from BGP to EIGRP due to hardware limitations, demonstrating adaptability
- Implemented defense-in-depth security following principle of least privilege
- Centralized critical services for simplified administration and troubleshooting
- Translated simulated design to working physical network, overcoming software limitations
Business Value Delivered
- Scalable Connectivity: Three-office network with expansion-ready design
- Enhanced Security: Segmentation, access control, and secure management
- Operational Efficiency: Centralized services and role-based management
Foundation for Systems Projects
This networking infrastructure represents the foundation that would host virtualized systems from other projects—demonstrating the full stack from physical network to application services.